Security is easy to talk about and hard to protect.A lot of startups build real security work into their product, but when it is time to file a patent, they describe it in a weak way. They say things like “secure login,” “encrypted storage,” or “role-based access.” That sounds fine on the surface. But in patent writing, broad labels do not do much by themselves. What matters is how your system actually works, what problem it solves, and what makes your approach different from the usual way.
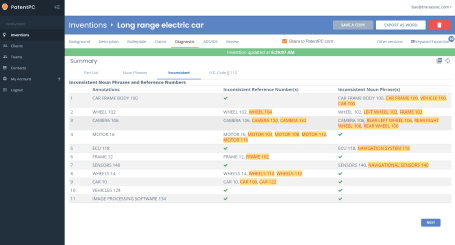
Why Most Security Patent Claims End Up Weak
Security sounds important in every pitch, every roadmap, and every board update. But when a company tries to protect that work with a patent, the write-up often becomes thin, vague, and easy to ignore.
That is not because the product lacks value. It is usually because the invention is described at the wrong level.
The business may have built something truly smart, but the patent draft talks about it in flat, generic terms that could apply to almost any software system.
This is where strong companies lose ground without even seeing it happen. They assume that because the feature is advanced, the patent claim will also be strong. In practice, that is rarely true.
Patent strength comes from precision. It comes from showing what the system does, why it does it that way, how the parts work together, and what practical gain comes from that design. When that story is missing, the claim becomes weak before it ever gets filed.
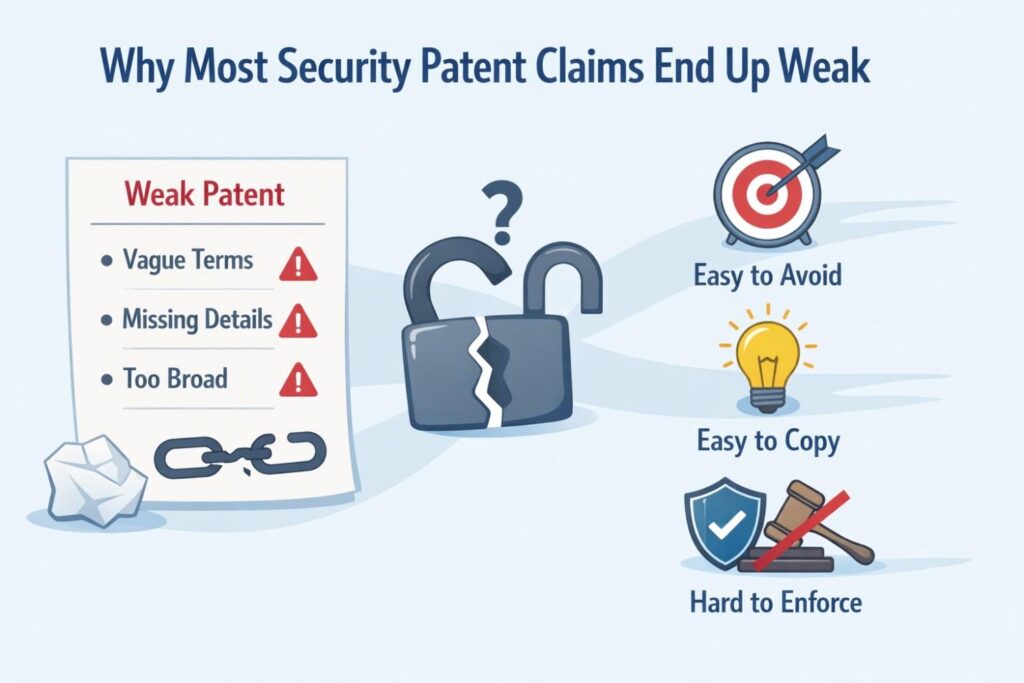
The problem starts when teams describe categories instead of systems
Many teams say they invented “multi-factor authentication,” “encrypted messaging,” or “fine-grained access control.” Those are categories. They are not inventions by themselves.
A category tells you what kind of feature exists. It does not explain the technical path the system takes or what makes that path different from the common way.
That gap matters more than most founders think. If your write-up stops at category words, it leaves out the real business value. It hides the engineering judgment that made the feature work in a better way.
It also makes it easier for others to argue that your claim is just a broad statement about a known idea.
A better approach is to move from label to mechanism. Do not stop at “we use auth.” Explain how identity signals are gathered, how trust is scored, how the session changes over time, and how access is granted or blocked under changing conditions.

The more your claim reflects the actual working system, the harder it is for someone else to dismiss it as generic.
The useful question is not “what feature do we have?”
After teams write a first draft, they often ask whether the feature sounds novel. That is not the best question. The better question is what the system is doing that another normal implementation would not do the same way.
That shift changes everything. It pushes the company to identify the design decisions that create business value. Maybe your product lowers fraud without increasing login drop-off.
Maybe it protects sensitive actions without forcing full re-auth every time. Maybe it uses encryption in a way that lets data stay useful while still protected. Those are invention paths. Those are also better starting points for claims.
Most weak claims are written too close to marketing language
Security products are often sold with polished terms. Trust. Privacy. Zero friction. Seamless control.
Enterprise-grade protection. Those phrases may help close deals, but they do almost nothing for a patent strategy. In fact, they can hurt the process if the patent draft copies the same style.
Marketing language hides the moving parts. It smooths over the exact steps that make the feature work.
A patent needs the opposite. It needs the rough edges. It needs the sequence, the checks, the conditions, the exceptions, and the technical tradeoffs. That is where the invention usually lives.
For businesses, this creates a clear action point. When you prepare invention notes, do not start from the sales deck. Start from the product spec, the architecture discussion, the security review notes, the support pain points, and the engineering debate that led to the final design.
Those sources contain the real differentiators. That is where strong claim material tends to hide.
Teams often focus on the lock, not the reason the lock exists
A common mistake is to describe the protection step while skipping the business problem that forced the design. This makes the claim feel thin because it lacks context.
It tells the reader what happens, but not why the approach matters.
The strongest security claims usually tie the mechanism to a real operating problem. Maybe the company needed to stop account takeovers in a shared-device setting.
Maybe the team had to enforce different access rights across machine agents, human admins, and external partners.

Maybe the product needed to protect keys in a fast edge environment without dragging down performance. When the claim is grounded in the actual problem, the invention becomes clearer and more defensible.
Business context makes the technical design easier to protect
This is not about adding fluff. It is about showing that the design was not random. A useful patent narrative explains that the company faced a real constraint and built a real solution around it.
That makes the invention look less like a general idea and more like a concrete technical answer.
For a business, this is strategic. It helps create claims that map to market pain. If a patent covers a security method tied to a painful and costly customer problem, it becomes more than a filing.
It becomes a business asset that supports product value, partner leverage, and future diligence conversations.
Founders often understate what their engineers actually invented
Technical teams are used to moving fast. They solve problems, push fixes, improve flows, and keep shipping.
Because of that pace, they often treat important design work like normal implementation effort. They do not pause and ask whether the solution itself is unusual.
This leads to weak claims because the patent draft only captures the surface feature, not the deeper architecture choices. The business ends up protecting the obvious part while missing the real differentiator.
That is a costly mistake, especially in security, where subtle design choices often create the biggest moat.
A practical way to avoid this is to ask engineers what they rejected before landing on the current design. The discarded paths are often very revealing. They show where the tradeoffs were hard.
They show what did not work. And they often highlight the exact insight that makes the final system inventive.
Many claims fail because they ignore the full security flow
A security feature is rarely one isolated step. It is usually a chain. One signal triggers a check. That check affects a score. The score changes access. Access changes session state.
Session state may affect key use, logging, or policy updates. When the claim only covers one piece in isolation, it can end up too narrow, too weak, or too easy to design around.
Businesses should care about this because competitors do not need to copy every detail to create risk. If your claim only covers one narrow checkpoint, another company may shift that checkpoint, reorder the sequence, or swap in a related signal and avoid the claim altogether.
That does not mean broad claiming is bad. It means the claim set should reflect the full flow and the most important variations.
Claim the motion, not just the object
A weak draft often claims a thing. A stronger draft often claims how the thing behaves across a sequence. This is especially true in auth, encryption, and access control.
Security is dynamic. Risk changes. Permissions change. Keys rotate. Sessions expire or step up. Devices drift from trusted to untrusted states.
When the patent captures that motion, it becomes more valuable. It reflects how the product really operates in the field.
It also makes the protection harder to sidestep because the claim follows the decision process, not just one static feature.
Generic words create a false sense of coverage
Some businesses feel safe when a claim sounds broad. They think broad language means broad protection.
In reality, broad and generic are not the same thing. A claim that uses loose terms without enough structure may look large on paper but collapse under review because it lacks technical grounding.
This is a dangerous trap for startups. They want efficiency, and they do not want a patent filled with too much detail that feels limiting. That instinct is understandable. But skipping detail at the start can make the whole filing fragile.
The better strategy is layered detail. Describe the core approach clearly, then support it with multiple technical versions, fallback designs, thresholds, signals, states, and deployment settings.
That gives room for broader claims while still grounding them in real engineering work. It is a stronger business move because it creates options later instead of forcing a weak one-size-fits-all draft.
Weak claims often miss where the value really sits
In many security systems, the value is not in the fact that a check occurs. The value sits in when the check occurs, what triggers it, what data is used, what the system does with the result, and how the system reduces burden on the user or operator. If the draft misses those details, it may capture a shell instead of the invention.
This matters because buyers, partners, and investors care about outcomes. They care that your product cuts risk, lowers support tickets, passes security review faster, or makes enterprise deployment easier.
A patent becomes stronger when it is tied to the mechanism that creates those outcomes.
Actionable advice for product and legal alignment
A very useful internal exercise is to have product, engineering, and whoever handles IP sit in one room and answer one question: what painful thing does this security design make easier without making another thing worse?
That framing pushes the team beyond generic feature talk. It forces clarity around the tradeoff the invention solved.
The answer might be that the system improves trust checks without slowing login. It might be that encryption can be enforced while keeping analytics usable.
It might be that access rules can change in real time without breaking existing sessions. Those statements are much closer to strong claim territory because they connect business benefit to technical structure.
Companies often describe the endpoint but not the decision logic
In access control claims, teams often say that a user is granted or denied access based on permissions. That is too shallow.
The real invention may be in how permissions are built, changed, inherited, limited, or overridden. It may be in how the system evaluates context before making the decision. It may be in how temporary rights are issued and then revoked.
Without that decision logic, the claim can sound like basic software behavior. With that logic, the claim starts to show a concrete technical method.
For businesses building modern products, this is especially important because access control is no longer simple role mapping.

Today it may involve device posture, time windows, workload type, data sensitivity, geographic restrictions, session risk, delegated authority, or policy conflict resolution. If your system handles that complexity in a novel way, that is likely where the valuable patent content sits.
How to Describe Auth, Encryption, and Access Control in a Patent
When a company builds security into its product, the hard part is often not the code. The hard part is turning that code into patent language that actually protects something useful.
Many teams know their system is strong. They know it solves a real problem. But when they sit down to describe it, they default to labels that are too broad, too plain, or too close to everyday security talk.
That is where value starts to slip away. A patent does not become strong just because the underlying product is advanced. It becomes strong when the write-up captures what the system really does, how it does it, and why that specific design matters.
With auth, encryption, and access control, this matters even more because these areas are crowded. Many products use them. Very few explain them well enough to claim the real invention.
Start with the exact security problem your system solves
Before you describe any technical flow, you need to frame the problem in a clean and practical way. Not a giant industry problem. Not a vague goal like “improve security.”
The real operating problem your team solved inside the product. This becomes the anchor for the whole section because it explains why the system exists and what the claimed design is trying to achieve.
A useful patent description often begins with tension. The system needed to protect something, but common approaches created too much friction, too much delay, too much false blocking, too much compute cost, or too much admin burden.
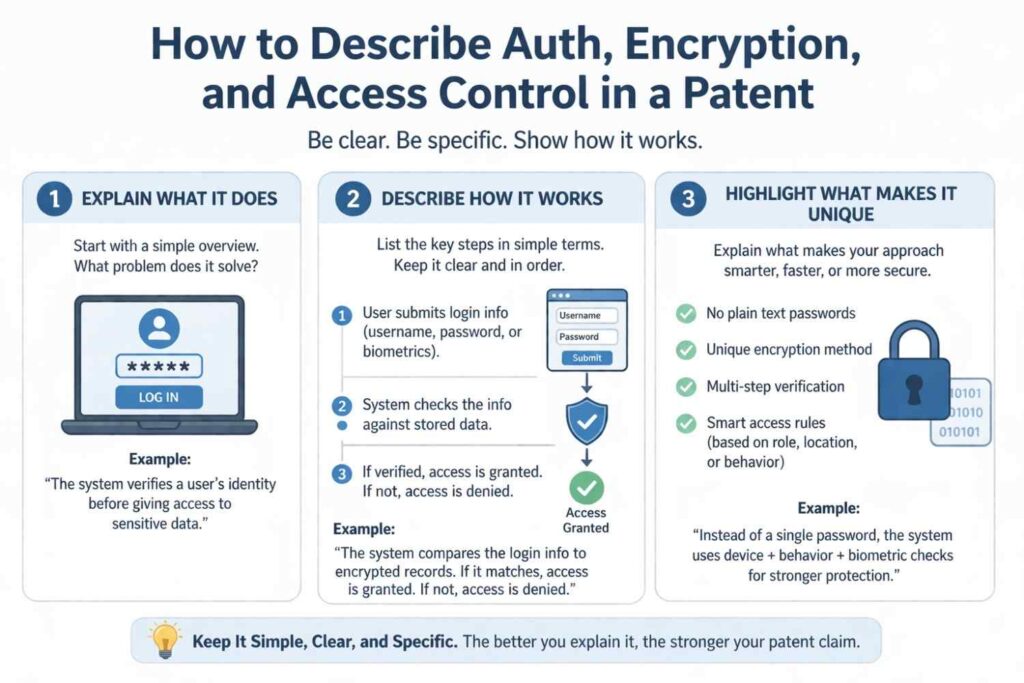
That tension makes the invention easier to understand. It tells the reader that the design was not random. It was built to solve a problem that mattered in real use.
Describe the system as a flow, not as a feature label
Many weak write-ups begin with a label such as “the system provides user authentication.” That statement is not wrong, but it does almost no work. It tells the reader the category of the feature, not the actual path the system takes.
Patents become much stronger when they describe movement. What enters the system, what gets checked, what gets generated, what changes, what gets stored, and what result follows.
This is especially important for security because security is rarely one step. A signal comes in. A rule gets evaluated. A threshold gets applied. A permission changes.
A key gets selected. A session gets limited. A log gets written. When you describe the whole motion, you show the invention in a more concrete way.
The flow should match how the product behaves in real life
This is not the place for abstract textbook language. It should sound like the actual system your team built. If the product checks device state before login challenge selection, say that.
If it derives temporary access scope from a mix of user role and data sensitivity, say that. If encrypted content is processed through a protected execution path before a policy decision is made, say that.
The point is to mirror reality. A patent description becomes more useful when it reflects the operating sequence the product actually uses. That is what helps protect business value instead of just documenting a generic idea.
Explain auth as a decision process, not just an identity check
Auth is often described too simply. Many teams reduce it to “verifying a user.” But modern auth systems usually do much more than confirm identity once and move on.
They evaluate risk, adjust challenge level, react to session behavior, compare device traits, and sometimes change trust over time. If your product works this way, the patent should make that clear.
The better framing is to treat auth as a sequence of decisions. The system receives one or more identity signals. It compares those signals against one or more trust conditions.
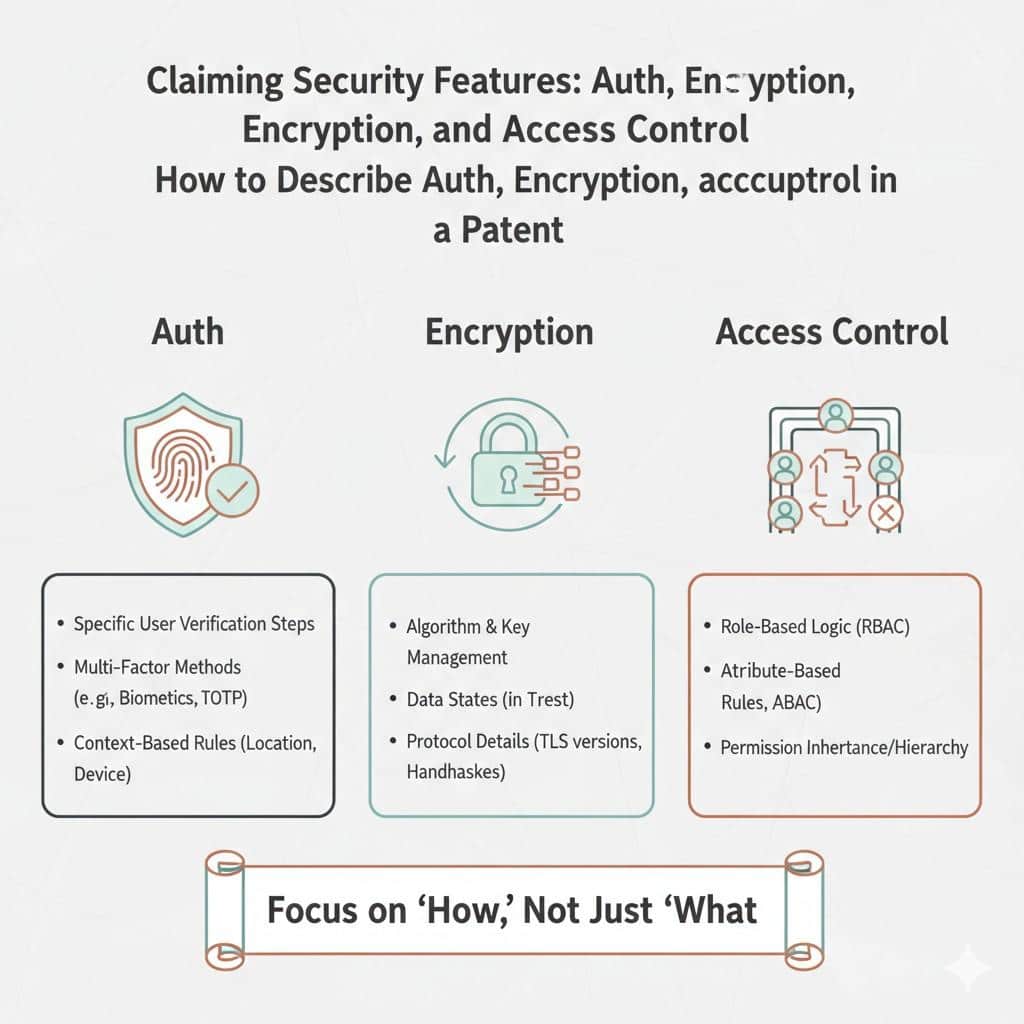
It selects a verification action, a session state, or a level of permitted activity based on the result. That is already much stronger than just saying the user logs in securely.
Show what the auth system uses to make its choice
A strong description does not only say that a decision happened. It says what the decision was based on.
This can include credentials, tokens, device posture, prior session history, user behavior, network conditions, resource sensitivity, or other signals the system uses to determine the next action.
These inputs matter because they reveal the practical design of the product. They also help show where the novelty may sit. In many cases, the invention is not the existence of a login step.
It is the specific combination of inputs and the way those inputs change what the system does next.
Include the step-up and step-down logic
One very useful area to describe is how the auth system changes its response over time. Some systems increase checks when risk rises. Others reduce friction when trust is already strong.
Some do both. If your product adjusts verification level during a session or before high-risk actions, that should be described clearly.
This matters because it turns auth from a static gate into a dynamic control system.
That is often where the most protectable material lives. It also reflects how good security products really work in practice, which makes the patent more aligned with business reality.
Describe encryption in terms of data handling, not just data hiding
A lot of patent drafts describe encryption as if the whole story is that data becomes unreadable to outsiders.
That is part of the story, but not the full value. In many software systems, the real invention is about how data moves before encryption, during encryption, after encryption, and under what conditions it can be used again.
For that reason, it helps to describe encryption through the life of the data. What kind of data is being protected. When it is transformed. Which key or key class is used.
Where the key comes from. What access conditions must exist before decryption or partial use is allowed. These details turn a plain statement into a system description.
Focus on key handling because that is often where the invention sits
Encryption claims become much stronger when they explain how keys are managed.
Many companies stop at saying data is encrypted with a key. But the interesting work may be in how keys are created, segmented, rotated, assigned to tenants, limited by workload, or tied to access context.
A business should pay close attention to this because key handling often creates both technical advantage and customer trust.
If your system reduces exposure by limiting key use to narrow contexts, or if it distributes key control in a special way across services, that may be far more valuable than the basic fact of encryption itself.
Explain how the system stays useful while data stays protected
One of the most important things to capture is how the product balances protection with utility. Businesses do not encrypt data just to lock it away forever.
They still need to search, analyze, share, sync, or enforce policies on that data. If your product found a better way to keep data usable while protected, that is often central to the invention.
This is where the patent should speak clearly. Describe the mechanism that lets the system preserve function without giving up control.
That may involve selective decryption, policy-gated access, transformed representations, secure intermediate processing, or context-based key release.
However your system does it, that bridge between protection and usefulness should be described in practical terms.
Describe access control as policy execution, not just permission assignment
Access control is often reduced to a simple sentence like “the user is allowed or denied access based on permissions.” That framing is too thin for most modern systems.
Today, access control often involves layered rules, changing conditions, temporary rights, data-specific limits, and policy evaluation that happens across services or environments.
A stronger patent description treats access control as a live policy engine. It explains how rights are assigned, checked, narrowed, inherited, revoked, or escalated. It also explains what factors influence those decisions.
This makes the section more accurate and more defensible because it captures the real operating logic behind the product.
Show how context changes access outcomes
One of the best ways to strengthen an access control description is to explain what context the system uses.
This might include user role, team status, device state, transaction type, document classification, workload origin, session risk, time window, or jurisdiction boundary.
The system may not grant access based on identity alone. It may combine identity with changing facts about the moment.
That is important because context-aware access is often much more valuable than static role mapping.

It helps companies reduce overexposure without blocking legitimate use. If your product does this in a clean and novel way, the patent should spell it out.
Temporary and conditional access deserve special attention
A lot of modern products issue access that is narrow, timed, scoped, or revocable under changing conditions. This is often more inventive than permanent permission assignment.
It also maps well to real business needs because companies want tighter control without creating constant manual work.
If your system generates temporary access tokens, applies action-specific rights, or revokes permissions when trust falls below a threshold, describe that sequence carefully.
This shows that the system is not just storing a permission table. It is actively managing access based on real conditions.
Use concrete actors, objects, and transitions
Patent writing gets stronger when the nouns are clear. Instead of vague phrases like “an entity” or “a secure item” used over and over, describe the real actors in the system.
That may be a user device, an identity service, a policy engine, a workload, a protected data object, a session manager, or a key controller. Clear naming makes the technical story easier to follow.
The same goes for actions. The write-up should make it easy to see when a token is issued, when a key is requested, when policy is checked, when a session state changes, and when access is granted or denied.
Those transitions are the bones of the invention. If they stay blurry, the whole section feels generic.
Include alternative implementations without losing focus
A strong patent section does not only describe one exact version of the system. It also gives room for close variations.
This matters because competitors may try to copy the core idea while changing one signal, one order of steps, or one deployment location. If the description supports only one narrow form, the claim set may have less room later.
The goal is not to flood the section with endless versions. The goal is to include meaningful alternatives that still preserve the core inventive concept. For example, an auth system may use one trust signal in one deployment and several in another.
An encryption system may assign keys per tenant in one case and per data class in another. An access control engine may evaluate policies locally in one architecture and through a remote decision service in another.
Variations should support the same core technical idea
This is the key discipline. Do not add random alternatives just to sound broad. Add versions that show the invention can be implemented in more than one practical form while keeping the same underlying logic.
That gives the patent room to grow without making the section feel scattered.
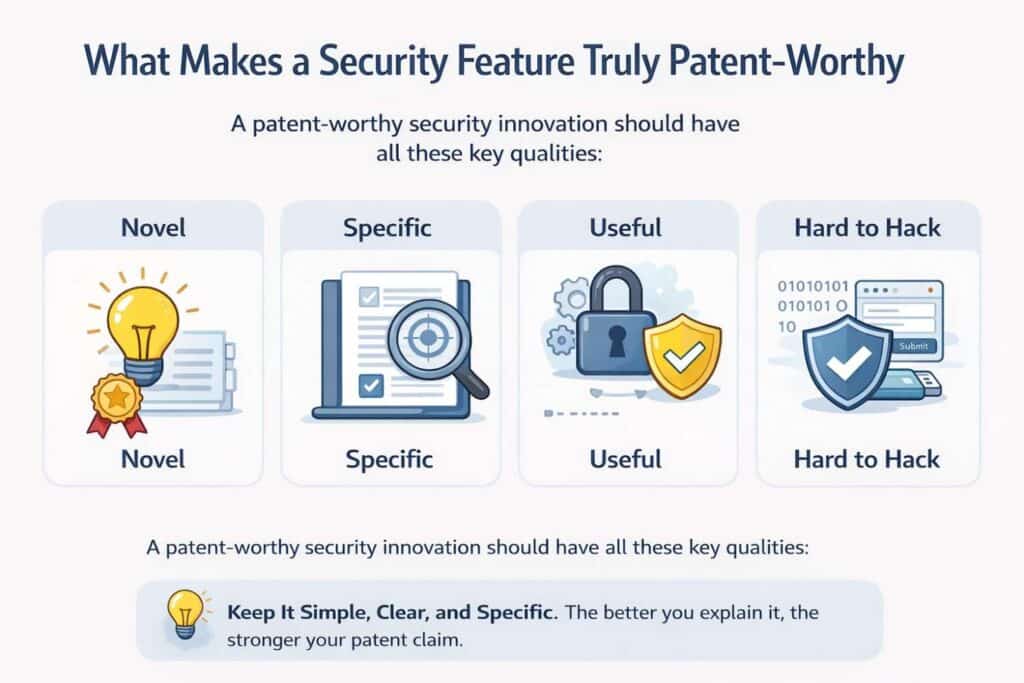
What Makes a Security Feature Truly Patent-Worthy
Not every security feature should become a patent. That is an important place to start.
A company may have strong security, good engineering, and clean product design, but that does not always mean there is a patentable invention inside it.
Many teams confuse “important” with “patent-worthy.” They are not the same. A feature can be useful, expected, and valuable to customers while still being too standard to support a strong patent position.
The real question is not whether the feature protects users. The real question is whether the company created a specific technical approach that solves a real problem in a way that is meaningfully different from the usual path.
That is what separates routine security work from protectable invention.
For startups and growth-stage companies, knowing that difference matters a lot. It helps them spend time on the right ideas, protect the right assets, and avoid filing around things that do not create lasting leverage.
Patent-worthy security starts with a real technical solution
A security feature becomes more interesting for patent purposes when it does more than apply a known rule. It needs to show that the team solved a technical problem with a technical design.
That sounds simple, but in practice it is where most businesses either gain real ground or waste effort.
A weak candidate is usually a standard security control added in a normal way. A stronger candidate is a system that changes how the control works in order to solve a practical problem the standard version handles poorly.
The difference may seem small at first, but it is usually where the value sits.
It may be the order of operations, the way signals are combined, the way risk is scored, the way permissions adapt, or the way encrypted data stays useful without becoming exposed.
The feature needs more than a label people already know
Words like authentication, encryption, and access control are too broad to mean much by themselves. Most products use them in some form. A patent-worthy feature is not “we added encryption.”
It is “we designed a particular encryption handling path that reduces exposure while preserving a needed function.”
It is not “we support access control.” It is “we built a context-driven permission model that updates rights during a live session without breaking system continuity.”
This matters for businesses because it changes how invention should be documented. Teams should stop asking whether a feature sounds advanced and start asking whether the implementation path reflects a distinct technical idea.
The product category will not carry the patent. The architecture and behavior will.
Novelty often hides in the design choice, not the feature name
This is where many companies miss good opportunities. They assume the innovation has to sound dramatic.
In reality, the strongest idea may be a subtle structural choice that solved a hard problem in an elegant way. It may not sound flashy in a demo, but it may be exactly the kind of thing that becomes valuable in a patent.
That is why founders should look closely at the moments where engineers had to make non-obvious decisions. Those moments often reveal the real invention. The key is not whether the feature seems exciting.
The key is whether the design choice would cause another strong technical team to stop and say that this is not the usual way to do it.
A patent-worthy feature solves a painful tradeoff
Many of the best security inventions come from tension. The team needed stronger protection, but common methods added too much friction. The product needed tighter access, but old models were too rigid.
Data needed to stay protected, but it still had to be processed, shared, or searched. These are the kinds of pressures that create patent-worthy solutions.

That is good news for businesses because the best patent opportunities often come from real product pain, not from research done in isolation. If your team had to solve a stubborn tradeoff in order to ship the product, there may be protectable value in that solution.
The tradeoff should be visible in the invention story
A patent-worthy feature usually has a before and after story. Before, the company faced a real limitation. After, the company created a system that improved one goal without destroying another.
That story gives shape to the invention. It helps explain why the approach matters and why it is more than routine implementation.
For example, an auth system may reduce false login blocks without reducing security strength. An encryption design may reduce key exposure without making the system too slow to use.
An access model may tighten control without burying admins in manual rules. When a security feature solves that kind of business-critical tension, it deserves a closer look.
Strong patent candidates make a compromise less painful
This is a very useful test. Ask whether the feature made an ugly compromise easier to live with or removed it altogether. If the answer is yes, there may be patent-worthy substance there.
If the answer is no, and the feature mostly applies known security practice in an ordinary way, it may not be the best filing target.
This way of thinking is highly practical for businesses. It helps product, engineering, and IP work from the same lens. It also keeps the company focused on protecting the work that actually changes customer value.
A security feature becomes stronger when it changes system behavior over time
Many weak patent candidates describe static rules. A user either has access or does not.
Data is either encrypted or not. A password is either correct or not. That kind of fixed logic is often too plain unless there is something unusual in how it is implemented.
Patent-worthy features often look more dynamic. The system adjusts challenge level based on risk. It narrows permissions after certain events. It changes trust as the session continues.
It releases or withholds key access based on context. It adapts security controls to changing state rather than applying one flat rule to every case.
This matters because dynamic behavior often reflects deeper engineering. It shows that the company built a real decision system, not just a one-time checkpoint. That is often more defensible and more valuable.
Adaptive logic can be a major sign of invention
A useful patent question is whether the security system reacts in a structured way to changing conditions. If it does, the next question is how. What inputs matter.
What thresholds exist. What transitions happen. What downstream effect follows. These details often reveal whether the feature is just configurable or truly inventive.
For businesses, this is where good internal interviews matter. Ask the team what conditions cause the system to act differently and why those rules were designed that way.
The answers often contain the exact language needed to identify whether the feature is truly patent-worthy.
A feature that learns, updates, or narrows may be more valuable than one that blocks
Many teams think in terms of blocking bad actions. But some of the most interesting security inventions do something more refined. They steer the system into a safer state without shutting it down.
They limit the scope of risk instead of forcing full denial. They preserve continuity while reducing exposure.

That kind of behavior is often commercially important because customers do not just want safety.
They want reliable use. A feature that improves both can be a very strong patent candidate because it reflects technical sophistication tied to business need.
Patent-worthy security usually has a clear internal mechanism
A feature may sound smart from the outside, but if the team cannot explain the mechanism in plain steps, the idea may not be ready. That does not always mean it lacks value.
It may just mean the invention has not been captured clearly enough. But mechanism matters. A patent-worthy feature should be describable as a system with parts, states, transitions, and outcomes.
That is true even when machine learning or broader automation is involved. The patent case does not rest on saying the system is intelligent.
It rests on showing what the system receives, how it processes those inputs, what conditions it evaluates, and what actions follow. Without that structure, the feature may sound impressive but still be too vague to protect well.
Clear mechanism is what turns engineering into IP
This is one of the most important business points in the whole discussion. Investors, buyers, and acquirers do not get much comfort from a vague statement that a startup uses advanced security.
They care more when the company can show it has built a specific system that creates a real advantage. A patent-worthy mechanism helps do that because it makes the innovation concrete.
The company should be able to explain the feature without hiding behind buzzwords. It should be able to say what happens first, what happens next, and why that sequence matters.
That kind of clarity is often the difference between a filing that sits in a folder and one that becomes a strategic asset.
If the team cannot map the flow, the filing may be early or weak
This is a simple but powerful screening tool. If the engineers cannot yet map the feature cleanly, the company may need to do more work before filing, or it may need help drawing the invention out of the product.
Either way, the answer is not to pad the draft with generic language. The answer is to identify the real mechanism first.
For fast-moving businesses, this is one reason process matters so much. The sooner the invention is captured while the architecture choices are still fresh, the easier it is to assess whether the feature is truly worth protecting.
Patent-worthy security creates a result that matters in the field
A feature becomes more compelling when it produces a practical outcome that customers, operators, or systems actually feel. That outcome does not need to be marketing language.
It should be operational. Fewer false denials. Lower credential exposure. Better tenant separation. Faster trust decisions. Safer cross-service access. More precise revocation. Less overbroad permission sprawl.
The reason this matters is simple. A patent is stronger as a business asset when it covers something tied to real-world gain. That makes the invention easier to position and easier to defend internally as worth the investment.
Wrapping It Up
Security features can look ordinary from the outside and still hold real patent value on the inside. That is the big idea behind this whole topic. Auth, encryption, and access control are used everywhere, so just saying your product has them does not do much. What matters is the way your system handles them, the problem your team solved, and the exact design choices that make your approach worth protecting.